Database:
A database is a collection of related data which represents some aspect of the real world. A database system is designed to be built and populated with data for a certain task.
Database Management System (DBMS)
Database Management System (DBMS) is a software for storing and retrieving users’ data while considering appropriate security measures. It consists of a group of programs which manipulate the database. The DBMS accepts the request for data from an application and instructs the operating system to provide the specific data. In large systems, a DBMS helps users and other
third-party software to store and retrieve data.
Database management systems were developed to handle the following difficulties of typical File-processing systems supported by conventional operating systems.
- Data redundancy and inconsistency
- Difficulty in accessing data
- Data isolation – multiple files and formats
- Integrity problems
- Atomicity of updates
- Concurrent access by multiple users
- Security problems
ER diagram:
- ER diagram or Entity Relationship diagram is a conceptual model that gives the graphical representation of the logical structure of the database.
- It shows all the constraints and relationships that exist among the different components.
- An ER diagram is mainly composed of following three components- Entity Sets, Attributes and Relationship Set.

- Roll_no is a primary key that can identify each entity uniquely.
- Thus, by using a student’s roll number, a student can be identified uniquely.
Entity Set:
An entity set is a set of the same type of entities.
- Strong Entity Set:
- A strong entity set is an entity set that contains sufficient attributes to uniquely identify all its entities.
- In other words, a primary key exists for a strong entity set.
- Primary key of a strong entity set is represented by underlining it.
- Weak Entity Set:
- A weak entity set is an entity set that does not contain sufficient attributes to uniquely identify its entities.
- In other words, a primary key does not exist for a weak entity set.
- However, it contains a partial key called a discriminator.
- Discriminator can identify a group of entities from the entity set.
- Discriminator is represented by underlining with a dashed line.
Relationship:
A relationship is defined as an association among several entities.
- Unary Relationship Set – Unary relationship set is a relationship set where only one entity set participates in a relationship set.
- Binary Relationship Set – Binary relationship set is a relationship set where two entity sets participate in a relationship set.
- Ternary Relationship Set – Ternary relationship set is a relationship set where three entity sets participate in a relationship set.
- N-ary Relationship Set – N-ary relationship set is a relationship set where ‘n’ entity sets participate in a relationship set.
Cardinality Constraint:
Cardinality constraint defines the maximum number of relationship instances in which an entity can participate.
● One-to-One Cardinality – An entity in set A can be associated with at most one entity in set B. An entity in set B can be associated with at most one entity in set A.
● One-to-Many Cardinality – An entity in set A can be associated with any number (zero or more) of entities in set B. An entity in set B can be associated with at most one entity in set A.
● Many-to-One Cardinality – An entity in set A can be associated with at most one entity in set B. An entity in set B can be associated with any number of entities in set A.
●Many-to-Many Cardinality – An entity in set A can be associated with any number (zero or more) of entities in set B. An entity in set B can be associated with any number (zero or more) of entities in set A.
Attributes:
Attributes are the descriptive properties which are owned by each entity of an Entity Set.
Types of Attributes:
- Simple Attributes – Simple attributes are those attributes which cannot be divided further.
Ex. Age - Composite Attributes – Composite attributes are those attributes which are composed of many other simple attributes.
Ex. Name, Address - Multi Valued Attributes – Multi valued attributes are those attributes which can take more than one value for a given entity from an entity set.
Ex. Mobile No, Email ID. - Derived Attributes – Derived attributes are those attributes which can be derived from other attribute(s).
Ex. Age can be derived from DOB. - Key Attributes – Key attributes are those attributes which can identify an entity uniquely in an entity set.
Ex. Roll No.
Constraints:
Relational constraints are the restrictions imposed on the database contents and
operations. They ensure the correctness of data in the database.
● Domain Constraint – Domain constraint defines the domain or set of values for an attribute. It specifies that the value taken by the attribute must be the atomic value from its domain.
● Tuple Uniqueness Constraint – Tuple Uniqueness constraint specifies that all the tuples must be necessarily unique in any relation.
● Key Constraint – All the values of the primary key must be unique. The value of the primary key must not be null.
● Entity Integrity Constraint – Entity integrity constraint specifies that no attribute of primary key must contain a null value in any relation.
● Referential Integrity Constraint – It specifies that all the values taken by the foreign key must either be available in the relation of the primary key or be null.
Closure of an Attribute Set:
The set of all those attributes which can be functionally determined from an attribute set is called a closure of that attribute set.
Keys: A key is a set of attributes that can identify each tuple uniquely in the given relation.
Types Of Keys:
- Super Key – A superkey is a set of attributes that can identify each tuple uniquely in the given relation. A super key may consist of any number of attributes.
- Candidate Key – A set of minimal attribute(s) that can identify each tuple uniquely in the given relation is called a candidate key.
- Primary Key – A primary key is a candidate key that the database designer selects while designing the database. Primary Keys are unique and NOT NULL.

- Alternate Key – Candidate keys that are left unimplemented or unused after implementing the primary key are called as alternate keys.
- Foreign Key – An attribute ‘X’ is called as a foreign key to some other attribute ‘Y’ when its values are dependent on the values of attribute ‘Y’. The relation in which attribute ‘Y’ is present is called as the referenced relation. The relation in which attribute ‘X’ is present is called as the referencing relation.
- Composite Key – A primary key composed of multiple attributes and not just a single attribute is called a composite key.
- Unique Key – It is unique for all the records of the table. Once assigned, its value cannot be changed i.e. it is non-updatable. It may have a NULL value.
Functional Dependency:
In any relation, a functional dependency α → β holds if- Two tuples having same value of attribute α also have same value for attribute β.
Types of Functional Dependency:
1.Trivial Functional Dependencies –
A functional dependency X → Y is said to be trivial if and only if Y ⊆ X. o Thus, if RHS of a functional dependency is a subset of LHS, then it is called a trivial functional dependency.
2. Non-Trivial Functional Dependencies –
A functional dependency X → Y is said to be non-trivial if and only if Y ⊄ X. o Thus, if there exists at least one attribute in the RHS of a functional dependency that is not a part of LHS, then it is called a non-trivial functional dependency.
Decomposition of a Relation:
The process of breaking up or dividing a single relation into two or more sub relations is called the decomposition of a relation.
Properties of Decomposition:
● Lossless Decomposition - Lossless decomposition ensures no information is lost from the original relation during decomposition. When
the sub relations are joined back, the same relation is obtained that was
decomposed.
● Dependency Preservation - Dependency preservation ensures None of the functional dependencies that hold on the original relation are lost. The sub relations still hold or satisfy the functional dependencies of the original
relation.
Types of Decomposition:
1.Lossless Join Decomposition:
- Consider there is a relation R which is decomposed into sub relations R1, R2, ….,Rn.
- This decomposition is called lossless join decomposition when the join of the sub relations results in the same relation R that was decomposed.
- For lossless join decomposition, we always have- R1 ⋈ R2 ⋈ R3 ……. ⋈ Rn = R where ⋈ is a natural join operator
2. Lossy Join Decomposition:
- Consider there is a relation R which is decomposed into sub relations R1, R2, ….,Rn.
- This decomposition is called lossy join decomposition when the join of the sub relations does not result in the same relation R that was decomposed.
- For lossy join decomposition, we always have- R1 ⋈ R2 ⋈ R3 ……. ⋈ Rn ⊃ R where ⋈ is a natural join operator
Normalization:
In DBMS, database normalization is a process of making the database consistent by-
● Reducing the redundancies
● Ensuring the integrity of data through lossless decomposition
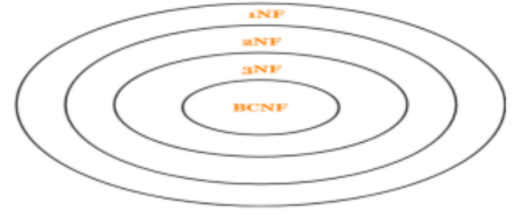
Normal Forms:
- First Normal Form (1NF) – A given relation is called in First Normal Form (1NF) if each cell of the table contains only an atomic value i.e. if the attribute of every tuple is either single valued or a null value.
- Second Normal Form (2NF) – A given relation is called in Second Normal Form (2NF) if and only if
- Relation already exists in 1NF.
- No partial dependency exists in the relation.
A → B is called a partial dependency if and only if- A is a subset of some candidate key and B is a non-prime attribute.
- Third Normal Form (3NF) – A given relation is called in Third Normal Form (3NF) if and only if
- Relation already exists in 2NF.
- No transitive dependency exists for non-prime attributes.
A → B is called a transitive dependency if and only if- A is not a super key and B is a non-prime attribute.
- Boyce-Codd Normal Form – A given relation is called in BCNF if and only if
- Relation already exists in 3NF.
- For each non-trivial functional dependency ‘A → B’, A is a super key of the relation.
Transaction: Transaction is a single logical unit of work formed by a set of operations.
Operations in Transaction:
● Read Operation – Read(A) instruction will read the value of ‘A’ from the database and will store it in the buffer in main memory.
● Write Operation – Write(A) will write the updated value of ‘A’ from the buffer to the database.
Transaction States:
- Active State –
- This is the first state in the life cycle of a transaction.
- A transaction is called in an active state as long as its instructions are getting executed.
- All the changes made by the transaction now are stored in the buffer in main memory.
- Partially Committed State –
- After the last instruction of the transaction has been executed, it enters into a partially committed state.
- After entering this state, the transaction is considered to be partially committed.
- It is not considered fully committed because all the changes made by the transaction are still stored in the buffer in main memory.
- Committed State –
- After all the changes made by the transaction have been successfully stored into the database, it enters into a committed state.
- Now, the transaction is considered to be fully committed.
- Failed State –
- When a transaction is getting executed in the active state or partially committed state and some failure occurs due to which it becomes impossible to continue the execution, it enters into a failed state.
- Aborted State –
- After the transaction has failed and entered into a failed state, all the changes made by it have to be undone.
- To undo the changes made by the transaction, it becomes necessary to roll back the transaction.
- After the transaction has rolled back completely, it enters into an aborted state.
- Terminated State –
- This is the last state in the life cycle of a transaction.
- After entering the committed state or aborted state, the transaction finally enters into a terminated state where its life cycle finally comes to an end.
ACID Properties:
To ensure the consistency of the database, certain properties are followed by all the transactions occurring in the system. These properties are called as ACID Properties of a transaction.
Atomicity –
o This property ensures that either the transaction occurs completely or it does not
occur at all.
o In other words, it ensures that no transaction occurs partially.
Consistency –
o This property ensures that integrity constraints are maintained.
o In other words, it ensures that the database remains consistent before and after the transaction.
Isolation –
o This property ensures that multiple transactions can occur simultaneously
without causing any inconsistency.
o The resultant state of the system after executing all the transactions is the same as the state that would be achieved if the transactions were executed serially one after the other.
Durability –
o This property ensures that all the changes made by a transaction after its successful execution are written successfully to the disk.
o It also ensures that these changes exist permanently and are never lost even if there occurs a failure of any kind.
Schedules:
The order in which the operations of multiple transactions appear for execution is called as a schedule.
Serial Schedules –
o All the transactions execute serially one after the other.
o When one transaction executes, no other transaction is allowed to execute.
o Serial schedules are always- Consistent, Recoverable, Cascadeless and Strict. ●
Non-Serial Schedules –
o Multiple transactions execute concurrently.
o Operations of all the transactions are inter leaved or mixed with each other.
o Non-serial schedules are not always- Consistent, Recoverable, Cascadeless and
Strict.
Serializability –
● Some non-serial schedules may lead to inconsistency of the database.
● Serializability is a concept that helps to identify which non-serial schedules are correct and will maintain the consistency of the database.
Serializable Schedules –
o If a given non-serial schedule of ‘n’ transactions is equivalent to some serial
schedule of ‘n’ transactions, then it is called as a serializable schedule.
o Serializable schedules are always- Consistent, Recoverable, Cascadeless and
Strict.
Types of Serializability –
● Conflict Serializability – If a given non-serial schedule can be converted into a serial schedule by swapping its non-conflicting operations, then it is called a conflict serializable schedule.
● View Serializability – If a given schedule is found to be viewed as equivalent to some serial schedule, then it is called a view serializable schedule.
Non-Serializable Schedules –
● A non-serial schedule which is not serializable is called a non-serializable schedule.
● A non-serializable schedule is not guaranteed to produce the same effect as produced by some serial schedule on any consistent database.
● Non-serializable schedules- may or may not be consistent, may or may not be
recoverable.
● Irrecoverable Schedules – If in a schedule,
o A transaction performs a dirty read operation from an uncommitted transaction
o And commits before the transaction from which it has read the value then such a
schedule is known as an Irrecoverable Schedule.
● Recoverable Schedules –If in a schedule,
o A transaction performs a dirty read operation from an uncommitted transaction
o And its commit operation is delayed till the uncommitted transaction either
commits or roll backs
then such a schedule is known as a Recoverable Schedule.
Types of Recoverable Schedules –
● Cascading Schedule – If in a schedule, failure of one transaction causes several other dependent transactions to rollback or abort, then such a schedule is called as a Cascading Schedule or Cascading Rollback or Cascading Abort.
● Cascadeless Schedule – If in a schedule, a transaction is not allowed to read a data item until the last transaction that has written it is committed or aborted, then such a schedule is called as a Cascadeless Schedule.
● Strict Schedule – If in a schedule, a transaction is neither allowed to read nor write a data item until the last transaction that has written it is committed or aborted, then such a schedule is called as a Strict Schedule.

File Structures:
● Primary Index: A primary index is an ordered file, records of fixed length with two fields. First field is the same as the primary key as a data file and the second field is a pointer to the data block, where the key is available. The average number of block accesses using index = log2Bi + 1, where Bi = number of index blocks.
● Clustering Index: Clustering index is created on data file whose records are physically ordered on a non-key field (called Clustering field).
● Secondary Index: Secondary index provides secondary means of accessing a file for which primary access already exists.
B Trees:
At every level , we have Key and Data Pointer and data pointer points to either block or record.
Properties of B-Trees:
Root of B-tree can have children between 2 and P, where P is Order of tree.
Order of tree – Maximum number of children a node can have.
Internal node can have children between ⌈ P/2 ⌉ and P
Internal node can have keys between ⌈ P/2 ⌉ – 1 and P-1
B+ Trees
In B+ trees, the structure of leaf and non-leaf are different, so their order is. Order of non-leaf will be higher as compared to leaf nodes. Searching time will be less in B+ trees, since it doesn’t have record pointers in non-leaf because of which depth will decrease.

Hi! I know this is somewhat off topic but I was wondering which blog platform are you using for this site? I’m getting tired of WordPress because I’ve had issues with hackers and I’m looking at options for another platform. I would be great if you could point me in the direction of a good platform.
Very nice style and good subject matter, absolutely nothing else we need : D.
Howdy! I just would like to give an enormous thumbs up for the good data you’ve right here on this post. I will likely be coming again to your weblog for extra soon.
When I originally commented I clicked the -Notify me when new comments are added- checkbox and now each time a comment is added I get four emails with the same comment. Is there any way you can remove me from that service? Thanks!
I believe you have mentioned some very interesting details , regards for the post.
Usually I don’t read article on blogs, however I would like to say that this write-up very compelled me to try and do so! Your writing style has been amazed me. Thanks, quite nice article.
Wonderful web site. Lots of useful information here. I¦m sending it to a few pals ans additionally sharing in delicious. And of course, thanks on your sweat!
Yeah bookmaking this wasn’t a risky conclusion great post! .
But wanna admit that this is very useful, Thanks for taking your time to write this.
Hi, Neat post. There is a problem together with your website in internet explorer, would check this?K IE still is the marketplace leader and a big component to other people will leave out your fantastic writing due to this problem.
I genuinely enjoy looking at on this site, it holds great content. “A short saying oft contains much wisdom.” by Sophocles.
Great amazing issues here. I?¦m very satisfied to peer your post. Thank you so much and i’m taking a look forward to touch you. Will you please drop me a e-mail?
Hi, I think your site might be having browser compatibility issues. When I look at your website in Safari, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, fantastic blog!
It¦s really a great and helpful piece of information. I am glad that you shared this useful info with us. Please keep us informed like this. Thanks for sharing.
Thanks for your personal marvelous posting! I really enjoyed reading it, you will be a great author.I will be sure to bookmark your blog and will come back down the road. I want to encourage continue your great posts, have a nice holiday weekend!
real cialis buy tadalafil 20mg generic gnc ed pills
I do agree with all the ideas you have presented in your post. They are very convincing and will definitely work. Still, the posts are very short for newbies. Could you please extend them a bit from next time? Thanks for the post.
Hello I am so delighted I found your blog page, I really found you by accident, while I was searching on Google for something else, Anyhow I am here now and would just like to say cheers for a marvelous post and a all round enjoyable blog (I also love the theme/design), I don’t have time to read it all at the minute but I have book-marked it and also added your RSS feeds, so when I have time I will be back to read more, Please do keep up the superb job.
buy cefadroxil medication duricef 250mg pills order proscar 1mg without prescription
purchase diflucan sale buy acillin without prescription order cipro for sale
estrace 1mg us prazosin online prazosin 2mg cheap
flagyl us order cephalexin 125mg generic cephalexin 125mg usa
brand vermox 100mg buy mebendazole generic cheap tadalis 20mg
buy cleocin pills for sale buy cleocin 300mg pills buy ed pills for sale
purchase avanafil pill generic diclofenac 100mg diclofenac 100mg generic
order indomethacin 75mg without prescription lamisil online order buy suprax 200mg sale
bimatoprost drug order desyrel 100mg online buy generic trazodone
order trimox 250mg generic buy arimidex 1mg without prescription order biaxin 250mg without prescription
order sildenafil suhagra order sildenafil 150mg
buy generic minocin buy terazosin 1mg pills order actos 30mg generic
isotretinoin 20mg over the counter isotretinoin 10mg brand azithromycin 250mg oral
cheap tadalafil 5mg cialis tadalafil 20mg generic tadalafil 5mg
azithromycin over the counter order prednisolone online buy cheap generic gabapentin
ivermectin covid natural ed pills order deltasone 10mg generic
order furosemide without prescription buy generic doxycycline online ventolin 4mg for sale
brand levitra 10mg order plaquenil 200mg hydroxychloroquine 200mg brand
order vardenafil 10mg for sale cost plaquenil order hydroxychloroquine online
asacol 800mg for sale astelin buy online oral irbesartan
olmesartan 10mg over the counter verapamil 120mg uk buy depakote 250mg
how to buy clobetasol buy buspirone 5mg order amiodarone 100mg online cheap
buy coreg sale buy aralen 250mg aralen 250mg drug
buy lanoxin online order molnupiravir 200 mg sale purchase molnupiravir online cheap
order naprosyn 500mg online cheap order lansoprazole 15mg pill order generic prevacid
olumiant uk glycomet 1000mg pills atorvastatin pills
albuterol 100 mcg pill cheap pyridium 200 mg order phenazopyridine sale
order montelukast 5mg online purchase montelukast generic order dapsone 100 mg pills
buy cheap adalat cheap allegra buy fexofenadine pills for sale
priligy medication order cytotec 200mcg pills xenical 60mg generic
buy metoprolol 50mg for sale metoprolol 50mg oral methylprednisolone 8mg otc
order diltiazem sale diltiazem 180mg cheap zyloprim 300mg uk
aristocort price purchase clarinex pill loratadine 10mg uk
order rosuvastatin 10mg generic rosuvastatin us motilium 10mg over the counter
buy ampicillin online buy ampicillin cheap buy metronidazole for sale
tetracycline for sale online buy baclofen 25mg generic buy lioresal pills for sale
bactrim sale generic cleocin 300mg cleocin 150mg price
Pretty! This was a really wonderful post. Thank you for your provided information.
buy toradol online cheap order inderal 10mg sale inderal for sale
erythromycin 250mg usa nolvadex online nolvadex us
buy clopidogrel for sale methotrexate where to buy purchase warfarin pills
purchase rhinocort sale buy generic bimatoprost buy bimatoprost generic
metoclopramide 10mg ca buy reglan 10mg without prescription order nexium 40mg capsules
robaxin online order suhagra 100mg tablet suhagra 100mg ca
order topiramate 100mg without prescription purchase levofloxacin generic levaquin 250mg pills
avodart brand zantac 150mg ca order generic meloxicam
buy sildenafil 50mg online sildenafil overnight estrace 2mg oral
buy celecoxib 100mg cheap ondansetron 8mg zofran 8mg drug
purchase lamotrigine pill buy prazosin 2mg online order prazosin 2mg pill
справки москва
order aldactone pill buy zocor 10mg generic buy valacyclovir generic
You’ve made some decent points there. I looked on the internet for more info about the issue and found most individuals will go along with your views on this site.
purchase tretinoin without prescription buy retin sale order avana 200mg online cheap
propecia 1mg canada propecia 1mg drug viagra 100mg canada
Attractive portion of content. I just stumbled upon your website and in accession capital to assert that I acquire in fact loved account your weblog posts. Any way I will be subscribing in your feeds or even I achievement you access consistently fast.
buy generic tadacip purchase indocin online cheap indocin 75mg tablet
cialis 40mg pill ed solutions buy ed pills cheap
buy terbinafine no prescription cefixime 100mg uk trimox cost
You really make it seem so easy together with your presentation however I find this topic to be really something which I feel I might never understand. It sort of feels too complicated and very large for me. I am looking forward in your next publish, I will try to get the cling of it!
Hello, I check your blogs regularly. Your story-telling style is awesome, keep doing what you’re doing!
cost azulfidine 500mg verapamil price verapamil 240mg ca
anastrozole over the counter buy arimidex online cheap cost catapres 0.1mg
Hi there friends, nice piece of writing and good arguments commented here, I am truly enjoying by these.
Hi, i feel that i saw you visited my web site so i got here to go back the prefer?.I am trying to find things to improve my site!I guess its ok to use some of your concepts!!
divalproex brand isosorbide 40mg for sale buy generic isosorbide for sale
buy meclizine generic order minomycin for sale order minocycline online cheap
buy azathioprine 25mg order azathioprine 50mg without prescription order telmisartan pills
Woah! I’m really enjoying the template/theme of this site. It’s simple, yet effective. A lot of times it’s very hard to get that “perfect balance” between user friendliness and visual appearance. I must say you have done a amazing job with this. Additionally, the blog loads extremely fast for me on Safari. Superb Blog!
where can i buy ed pills buy generic sildenafil 50mg sildenafil usa
order molnunat 200mg generic purchase cefdinir pill cost omnicef 300 mg
how to buy prevacid purchase protonix without prescription protonix for sale
This design is wicked! You certainly know how to keep a reader entertained. Between your wit and your videos, I was almost moved to start my own blog (well, almost…HaHa!) Wonderful job. I really enjoyed what you had to say, and more than that, how you presented it. Too cool!
buy ed medications online viagra next day delivery usa cost tadalafil
Hey I know this is off topic but I was wondering if you knew of any widgets I could add to my blog that automatically tweet my newest twitter updates. I’ve been looking for a plug-in like this for quite some time and was hoping maybe you would have some experience with something like this. Please let me know if you run into anything. I truly enjoy reading your blog and I look forward to your new updates.
You really make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I will try to get the hang of it!
pills for ed buy tadalafil 10mg online order cialis 10mg sale
When I originally commented I seem to have clicked the -Notify me when new comments are added- checkbox and now every time a comment is added I recieve four emails with the same comment. Is there a means you can remove me from that service? Many thanks!
order avlosulfon 100mg generic buy dapsone paypal order perindopril 4mg pills
If you are going for most excellent contents like I do, simply visit this web site daily because it provides quality contents, thanks
fexofenadine 180mg generic cost ramipril amaryl 1mg over the counter
My spouse and I stumbled over here coming from a different web page and thought I might as well check things out. I like what I see so now i’m following you. Look forward to exploring your web page for a second time.
buy hytrin 1mg online leflunomide 10mg pills cialis prices
arcoxia price buy azelastine nasal spray for sale buy azelastine 10ml sprayers
It’s an remarkable article designed for all the web users; they will take benefit from it I am sure.
cordarone price amiodarone 200mg price order phenytoin generic
irbesartan 150mg cost avapro 150mg brand buy buspar 10mg sale
This design is wicked! You certainly know how to keep a reader entertained. Between your wit and your videos, I was almost moved to start my own blog (well, almost…HaHa!) Fantastic job. I really enjoyed what you had to say, and more than that, how you presented it. Too cool!
buy albenza sale order abilify 30mg without prescription buy provera 5mg generic
buy ditropan generic order oxytrol for sale alendronate order online
Hi there, I check your blogs regularly. Your writing style is awesome, keep doing what you’re doing!
You made some good points there. I looked on the web to learn more about the issue and found most individuals will go along with your views on this site.
Hi there, always i used to check webpage posts here early in the morning, as i love to learn more and more.
praziquantel for sale hydrochlorothiazide 25 mg tablet buy periactin
buy macrodantin 100 mg pills motrin 600mg canada order nortriptyline 25 mg for sale
I’ve read some just right stuff here. Definitely worth bookmarking for revisiting. I wonder how much attempt you put to create any such magnificent informative site.
buy luvox 50mg generic nizoral 200 mg ca order duloxetine 40mg sale
Hi my family member! I want to say that this article is awesome, great written and come with almost all significant infos. I’d like to peer more posts like this .
No matter if some one searches for his necessary thing, so he/she wants to be available that in detail, so that thing is maintained over here.
order glipizide 5mg glucotrol online buy purchase betamethasone creams
Why users still use to read news papers when in this technological world everything is existing on net?
order anafranil 25mg online cheap purchase progesterone sale buy prometrium 200mg without prescription
Excellent post. I was checking continuously this blog and I am impressed! Very useful information specially the last part 🙂 I care for such info a lot. I was seeking this particular info for a long time. Thank you and good luck.
buy prograf online cheap buy remeron cheap generic requip
brand tindamax 500mg tinidazole us buy bystolic 5mg without prescription
how to buy calcitriol buy fenofibrate 160mg online cheap buy fenofibrate 160mg generic
buy diovan cheap buy ipratropium for sale ipratropium for sale online
Truly no matter if someone doesn’t understand after that its up to other users that they will help, so here it happens.
trileptal 300mg us generic ursodiol 150mg actigall 300mg cheap
buy decadron generic cost linezolid 600 mg buy nateglinide
I’ve been exploring for a little bit for any high-quality articles or blog posts in this kind of area . Exploring in Yahoo I at last stumbled upon this web site. Reading this info So i’m satisfied to express that I have a very just right uncanny feeling I came upon exactly what I needed. I such a lot undoubtedly will make certain to don?t put out of your mind this web site and give it a look on a continuing basis.
I’m not sure why but this web site is loading extremely slow for me. Is anyone else having this issue or is it a problem on my end? I’ll check back later and see if the problem still exists.
buy bupropion paypal brand cetirizine 5mg strattera 10mg tablet
Your means of describing everything in this post is actually pleasant, all can easily understand it, Thanks a lot.
captopril 25mg cheap order generic atacand carbamazepine without prescription
Pretty nice post. I just stumbled upon your blog and wanted to say that I have really enjoyed browsing your blog posts. In any case I’ll be subscribing to your feed and I hope you write again soon!
I love your blog.. very nice colors & theme. Did you design this website yourself or did you hire someone to do it for you? Plz answer back as I’m looking to design my own blog and would like to know where u got this from. thank you
brand ciprofloxacin buy generic duricef online duricef order online
order quetiapine pill buy escitalopram 10mg without prescription buy escitalopram 20mg online
whoah this blog is magnificent i really like reading your articles. Stay up the good work! You recognize, a lot of people are searching around for this info, you can help them greatly.
Aw, this was a very nice post. Finding the time and actual effort to create a great article but what can I say I put things off a lot and never seem to get anything done.
buy lamivudine no prescription purchase zidovudine online accupril online order
Great site. Lots of useful information here. I’m sending it to some pals ans also sharing in delicious. And of course, thank you on your effort!
buy prozac 20mg generic naltrexone over the counter buy femara 2.5mg for sale
What’s up Dear, are you truly visiting this web site daily, if so then you will definitely get good experience.
frumil online buy purchase zovirax generic where can i buy acivir
It’s really a nice and helpful piece of information. I’m glad that you simply shared this helpful info with us. Please stay us informed like this. Thank you for sharing.
It’s really a nice and helpful piece of information. I’m glad that you simply shared this helpful info with us. Please stay us informed like this. Thank you for sharing.
order bisoprolol 5mg online order lozol brand oxytetracycline
cheap valaciclovir buy valaciclovir pills for sale cost floxin 400mg
cefpodoxime where to buy theophylline medication order flixotide generic
Incredible! This blog looks exactly like my old one! It’s on a completely different topic but it has pretty much the same layout and design. Great choice of colors!
order keppra pill where can i buy cotrimoxazole buy viagra 100mg generic
Роскошный мужской эромассаж Москва в спа салоне
I got this website from my pal who told me regarding this web site and now this time I am visiting this web site and reading very informative posts at this place.
buy zaditor generic cost ziprasidone order imipramine 25mg
how to get cialis sildenafil 50mg price buy sildenafil
I love reading through a post that will make people think. Also, thank you for allowing me to comment!
I am truly pleased to read this blog posts which includes plenty of helpful data, thanks for providing such information.
acarbose pills order precose 25mg griseofulvin 250mg drug
buy minoxytop buy tamsulosin 0.2mg generic buying ed pills online
Hi mates, how is everything, and what you wish for to say regarding this piece of writing, in my view its truly awesome in favor of me.
Hello there, just became aware of your blog through Google, and found that it is really informative. I’m gonna watch out for brussels. I will appreciate if you continue this in future. A lot of people will be benefited from your writing. Cheers!
I really like what you guys are usually up too. Such clever work and coverage! Keep up the good works guys I’ve you guys to our blogroll.
order aspirin 75mg pill buy generic eukroma buy imiquad medication
Very excellent info can be found on weblog. “You have to learn that if you start making sure you feel good, everything will be okay.” by Ruben Studdard.
Very well written post. It will be useful to anybody who employess it, as well as yours truly :). Keep up the good work – for sure i will check out more posts.
Wow, incredible blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is fantastic, let alone the content!
buy dipyridamole 25mg for sale buy pravachol without a prescription buy generic pravachol
buy meloset medication buy danocrine 100mg buy danocrine online
Great post.
duphaston brand dydrogesterone 10mg without prescription cost jardiance 10mg
fludrocortisone usa order imodium 2 mg for sale loperamide 2mg without prescription
hi!,I really like your writing so so much! percentage we keep in touch more approximately your post on AOL? I need an expert in this area to unravel my problem. May be that is you! Taking a look forward to see you.
I visited several websites except the audio quality for audio songs present at this website is really wonderful.
prasugrel pill purchase detrol online order detrol pills
order etodolac 600 mg pills order colospa 135mg pills buy cilostazol 100 mg generic
purchase ferrous generic how to buy ascorbic acid order betapace 40mg
If you wish for to get a great deal from this piece of writing then you have to apply such techniques to your won weblog.
Magnificent beat ! I wish to apprentice even as you amend your site, how can i subscribe for a blog web site? The account aided me a appropriate deal. I have been tiny bit familiar of this your broadcast provided brilliant transparent concept
pyridostigmine ca cost rizatriptan 10mg purchase maxalt for sale
buy enalapril 5mg for sale buy generic casodex 50mg buy duphalac for sale
My relatives always say that I am wasting my time here at net, but I know I am getting familiarity daily by reading such pleasant articles or reviews.
Magnificent goods from you, man. I’ve keep in mind your stuff prior to and you’re simply too wonderful. I really like what you’ve got here, really like what you’re stating and the best way in which you are saying it. You are making it entertaining and you still take care of to stay it sensible. I can not wait to read far more from you. This is actually a great site.
buy betahistine 16mg without prescription buy probenecid 500 mg for sale order probenecid 500mg online
This is very interesting, You are a very skilled blogger. I have joined your feed and look forward to seeking more of your great post. Also, I have shared your web site in my social networks!
buy xalatan medication rivastigmine 3mg uk rivastigmine tablet
Hello there! This article couldn’t be written any better! Going through this post reminds me of my previous roommate! He always kept talking about this. I will forward this article to him. Pretty sure he’ll have a good read. Thank you for sharing!
omeprazole order buy metoprolol 100mg pills order lopressor 50mg without prescription
cost premarin 0.625mg order sildenafil pill viagra 100mg brand
Greetings from Idaho! I’m bored to death at work so I decided to check out your site on my iphone during lunch break. I enjoy the info you present here and can’t wait to take a look when I get home. I’m shocked at how quick your blog loaded on my cell phone .. I’m not even using WIFI, just 3G .. Anyhow, superb site!
I always used to read post in news papers but now as I am a user of internet thus from now I am using net for articles or reviews, thanks to web.
telmisartan 80mg brand buy plaquenil for sale buy cheap generic molnunat
Wow, marvelous blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your site is fantastic, let alone the content!
Hello, just wanted to say, I liked this article. It was practical. Keep on posting!
cenforce order cenforce 100mg sale chloroquine online buy
buy tadalafil 20mg pills brand viagra 50mg cheap viagra pills
It’s awesome in support of me to have a web site, which is helpful for my experience.
thanks admin
After looking into a few of the blog articles on your website, I honestly like your way of blogging. I added it to my bookmark website list and will be checking back soon. Take a look at my web site as well and let me know how you feel.
omnicef 300 mg cheap buy cefdinir 300 mg generic prevacid 15mg cost
Hi, i think that i saw you visited my website so i came to return the favor.I am trying to find things to improve my website!I suppose its ok to use some of your ideas!!
Thanks for every other magnificent article. Where else may anybody get that kind of information in such a perfect means of writing?
I’ve a presentation subsequent week, and I am on the look for such info.
order provigil 100mg without prescription order phenergan buy prednisone online
You really make it seem so easy with your presentation however I find this topic to be really something which I feel I would never understand. It sort of feels too complicated and very wide for me. I am looking forward in your next post, I will try to get the cling of it!
WOW just what I was searching for. Came here by searching for %keyword%
order generic accutane 40mg zithromax for sale zithromax 500mg price
What’s up, yup this piece of writing is truly pleasant and I have learned lot of things from it regarding blogging. thanks.
order atorvastatin 20mg without prescription buy norvasc 10mg without prescription amlodipine over the counter
oral azipro 250mg order prednisolone 40mg without prescription purchase neurontin online
WOW just what I was searching for. Came here by searching for hair replacement options
buy protonix generic buy phenazopyridine paypal buy pyridium 200mg online
I’m impressed, I must say. Rarely do I encounter a blog that’s equally educative and engaging, and let me tell you, you have hit the nail on the head. The issue is something not enough folks are speaking intelligently about. I’m very happy that I found this in my search for something relating to this.
casino online games for real money best online casinos that payout furosemide 100mg price
Great goods from you, man. I’ve remember your stuff prior to and you’re simply too great. I really like what you’ve received here, really like what you’re stating and the best way through which you are saying it. You are making it entertaining and you still take care of to stay it smart. I can not wait to read far more from you. This is actually a terrific website.
What’s up it’s me, I am also visiting this web site daily, this site is in fact pleasant and the users are actually sharing pleasant thoughts.
Nice post. I was checking continuously this blog and I am impressed! Very useful information specially the last part 🙂 I care for such info a lot. I was seeking this particular info for a long time. Thank you and good luck.
online roulette free free blackjack buy ventolin without prescription
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but other than that, this is wonderful blog. An excellent read. I’ll definitely be back.
My programmer is trying to persuade me to move to .net from PHP. I have always disliked the idea because of the expenses. But he’s tryiong none the less. I’ve been using Movable-type on a number of websites for about a year and am worried about switching to another platform. I have heard fantastic things about blogengine.net. Is there a way I can transfer all my wordpress content into it? Any kind of help would be really appreciated!
amantadine 100 mg canada purchase avlosulfon without prescription dapsone 100 mg brand
casino slot games spins real money ivermectin drug
Hi, after reading this awesome article i am too glad to share my familiarity here with mates.
free spins casino order augmentin 1000mg synthroid 150mcg over the counter
Hi, I do believe this is an excellent web site. I stumbledupon it 😉 I’m going to come back once again since I book marked it. Money and freedom is the best way to change, may you be rich and continue to help other people.
medrol 8 mg for sale order adalat 30mg online aristocort 10mg pill
Link exchange is nothing else but it is only placing the other person’s blog link on your page at appropriate place and other person will also do same in favor of you.
buy serophene for sale clomid online imuran 50mg cheap
Guest Star supports video but it will also allow creators to host voice-only streams
Добро пожаловать на сайт онлайн казино, мы предлагаем уникальный опыт для любителей азартных игр.
I was wondering if you ever considered changing the page layout of your site? Its very well written; I love what youve got to say. But maybe you could a little more in the way of content so people could connect with it better. Youve got an awful lot of text for only having one or two images. Maybe you could space it out better?
I do accept as true with all the ideas you have presented on your post. They are very convincing and will definitely work. Still, the posts are too brief for novices. May just you please extend them a bit from next time? Thank you for the post.
vardenafil 20mg sale vardenafil 20mg over the counter buy tizanidine generic
Онлайн казино отличный способ провести время, главное помните, что это развлечение, а не способ заработка.
В нашем онлайн казино вы найдете широкий спектр слотов и лайв игр, присоединяйтесь.
buy generic perindopril over the counter desloratadine 5mg canada order fexofenadine pills
Hey there, I think your website might be having browser compatibility issues. When I look at your blog in Chrome, it looks fine but when opening in Internet Explorer, it has some overlapping. I just wanted to give you a quick heads up! Other then that, amazing blog!
dilantin 100mg over the counter dilantin 100 mg us oxybutynin 2.5mg oral
buy cheap generic claritin claritin sale oral priligy
generic baclofen 10mg buy elavil paypal buy toradol tablets
I relish, lead to I found exactly what I used to be taking a look for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
Please let me know if you’re looking for a article writer for your weblog. You have some really great posts and I believe I would be a good asset. If you ever want to take some of the load off, I’d really like to write some articles for your blog in exchange for a link back to mine. Please blast me an e-mail if interested. Many thanks!
order baclofen 10mg generic amitriptyline canada ketorolac us
order amaryl 4mg online cheap buy arcoxia 60mg buy etoricoxib 120mg for sale
Someone necessarily help to make seriously articles I would state. This is the first time I frequented your web page and to this point? I amazed with the research you made to create this actual publish incredible. Wonderful activity!
fosamax 70mg oral furadantin pill buy macrodantin medication
Its like you read my mind! You seem to know so much about this, like you wrote the book in it or something. I think that you could do with some pics to drive the message home a bit, but other than that, this is great blog. An excellent read. I’ll definitely be back.
buy inderal pills for sale buy inderal 10mg order plavix 75mg online cheap
I am extremely impressed with your writing skills and also with the layout on your blog. Is this a paid theme or did you customize it yourself? Either way keep up the nice quality writing, it’s rare to see a nice blog like this one these days.
I enjoy what you guys are up too. This sort of clever work and coverage! Keep up the superb works guys I’ve added you guys to blogroll.
purchase nortriptyline generic panadol 500 mg without prescription paracetamol 500mg sale
Wow! This blog looks exactly like my old one! It’s on a entirely different topic but it has pretty much the same layout and design. Wonderful choice of colors!
xenical online order buy mesalamine 800mg pills buy diltiazem 180mg for sale
buy warfarin cheap coumadin 5mg cost order reglan
I read this piece of writing fully about the comparison of most up-to-date and previous technologies, it’s remarkable article.
astelin ca buy irbesartan sale cost irbesartan 300mg
Хотите получить идеально ровный пол в своей квартире или офисе? Обратитесь к профессионалам на сайте styazhka-pola24.ru! Мы предоставляем услуги по устройству стяжки пола в Москве и области, а также гарантиру
снабжение строительных объектов москва
Хотите получить идеально ровный пол без лишних затрат? Обратитесь к профессионалам на сайте styazhka-pola24.ru! Мы предоставляем услуги по стяжке пола м2 по доступной стоимости, а также устройству стяжки пола под ключ в Москве и области.
famotidine drug purchase cozaar online buy tacrolimus 1mg for sale
We are a group of volunteers and starting a new scheme in our community. Your site provided us with useful information to work on. You have performed an impressive task and our whole group will probably be grateful to you.
Переставьте сомнения в сторону и обратитесь к профессионалам. механизированная штукатурка с mehanizirovannaya-shtukaturka-moscow.ru – это ваш путь к ровным и гладким стенам.
esomeprazole 40mg oral esomeprazole 40mg drug buy topiramate 100mg without prescription
oral zyloprim rosuvastatin online buy buy crestor 20mg for sale
buy imitrex levofloxacin generic where can i buy dutasteride
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You clearly know what youre talking about, why waste your intelligence on just posting videos to your site when you could be giving us something enlightening to read?
buspirone 10mg cheap buy buspar 5mg pills cordarone 200mg tablet
cost ranitidine zantac for sale celecoxib for sale online
motilium online buy cheap sumycin 250mg buy tetracycline 250mg
Hi friends, how is all, and what you desire to say about this piece of writing, in my view its really awesome for me.
Hi there terrific blog! Does running a blog similar to this take a lot of work? I have virtually no knowledge of computer programming but I was hoping to start my own blog soon. Anyways, if you have any recommendations or tips for new blog owners please share. I know this is off topic but I just needed to ask. Thank you!
brand flomax 0.4mg buy generic zocor online simvastatin 20mg cost
Hey! Do you know if they make any plugins to protect against hackers? I’m kinda paranoid about losing everything I’ve worked hard on. Any recommendations?
academic writing blog online essay writing write research paper
Thanks for a marvelous posting! I quite enjoyed reading it, you may be a great author.I will be sure to bookmark your blog and will come back in the foreseeable future. I want to encourage continue your great job, have a nice afternoon!
Hello there! This post couldn’t be written any better! Reading this post reminds me of my old room mate! He always kept talking about this. I will forward this article to him. Pretty sure he will have a good read. Thank you for sharing!
Когда нужно качество и быстрота, вам необходима механизированная штукатурка. Узнайте больше на mehanizirovannaya-shtukaturka-moscow.ru и обновите ваше пространство.
sildenafil buy online aurogra medication order estrace 1mg without prescription
buy cheap forcan buy diflucan 100mg generic purchase baycip pill
buy generic lamictal purchase lamictal pills buy mebendazole online
flagyl 200mg canada purchase septra keflex oral
Hello! I just want to give you a huge thumbs up for the great info you’ve got here on this post. I’ll be coming back to your website for more soon.
buy retin tablets buy tadalafil 20mg online cheap avanafil usa
clindamycin cost buy generic cleocin 150mg sildenafil over the counter
I think this is one of the most significant information for me. And i’m glad reading your article. But wanna remark on few general things, The website style is ideal, the articles is really nice : D. Good job, cheers
nolvadex usa order tamoxifen 10mg rhinocort cost
order tadacip 20mg for sale indomethacin 75mg cheap oral indomethacin
cefuroxime sale buy generic careprost online brand methocarbamol 500mg
terbinafine cost purchase terbinafine online gambling casinos
buy generic trazodone clindamycin over the counter clindamycin order
Great delivery. Solid arguments. Keep up the good effort.
professional paper writers advertisements to write essays on suprax 200mg oral
Good write-up. I certainly love this website. Continue the good work!
Appreciate the recommendation. Let me try it out.
college essay assistance free spins no deposit win real money casino games online
buy trimox 500mg generic arimidex online buy biaxin 500mg pills
rocaltrol generic purchase fenofibrate online order tricor 200mg generic
clonidine over the counter brand antivert 25 mg spiriva price
best topical acne medication prescription buy oxcarbazepine sale buy trileptal sale
P Enflasyon Ne Demek?
minocycline order online purchase minocycline pills cost ropinirole 1mg
how to buy uroxatral acid reflux drugs prescription list what is treatment of heartburn
buy femara 2.5 mg generic cost letrozole 2.5 mg aripiprazole 30mg ca
Spot on with this write-up, I seriously think this site needs a lot more attention. I’ll probably be back again to read more, thanks for the info!
strong natural sleeping pills sleeping pills for sale uk online weight loss medication clinic
Hurrah! Finally I got a webpage from where I be able to truly get helpful information regarding my study and knowledge.
hey there and thank you for your information I’ve definitely picked up anything new from right here. I did however expertise a few technical issues using this web site, since I experienced to reload the web site many times previous to I could get it to load properly. I had been wondering if your hosting is OK? Not that I am complaining, but sluggish loading instances times will very frequently affect your placement in google and can damage your quality score if advertising and marketing with Adwords. Anyway I’m adding this RSS to my e-mail and can look out for a lot more of your respective fascinating content. Make sure you update this again soon.
provera 10mg us buy hydrochlorothiazide generic purchase microzide without prescription
pills to quit smoking cigarettes medication becoming reliant on nicotine strongest non narcotic pain medicine
cyproheptadine 4mg tablet order ketoconazole 200mg pill ketoconazole without prescription
I don’t know if it’s just me or if everyone else experiencing problems with your website. It seems like some of the text within your posts are running off the screen. Can someone else please comment and let me know if this is happening to them too? This might be a problem with my browser because I’ve had this happen before. Cheers
number of approved antivirals daily medication for hsv 2 safe diet pill for diabetics
Hi, Neat post. There is a problem with your web site in internet explorer, may check this? IE still is the marketplace leader and a large portion of folks will miss your wonderful writing due to this problem.
brand cymbalta 20mg glucotrol 5mg brand buy provigil online
over the counter antifungal supplements most popular blood pressure meds safest bp meds for seniors
phenergan online buy buy stromectol 3mg pills ivermectin 3mg over counter
ulcer healing drugs duodenal ulcer pain aggravated by best pain killer for uti
I’m really enjoying the design and layout of your blog. It’s a very easy on the eyes which makes it much more enjoyable for me to come here and visit more often. Did you hire out a designer to create your theme? Excellent work!
I’m really enjoying the design and layout of your site. It’s a very easy on the eyes which makes it much more enjoyable for me to come here and visit more often. Did you hire out a designer to create your theme? Great work!
prednisone price buy amoxil 250mg online cheap buy generic amoxil 1000mg
do pharmacies sell birth control birth control refill online is hims safe to use
heartburn pills over the counter best antibloating gas heartburn product causes of excessive smelly flatulence
oral zithromax buy cheap zithromax neurontin 100mg price
FitSpresso is a special supplement that makes it easier for you to lose weight. It has natural ingredients that help your body burn fat better.
Greetings! Very helpful advice within this article! It is the little changes that produce the biggest changes. Thanks a lot for sharing!
order urso for sale purchase zyrtec generic zyrtec 10mg over the counter
strattera 10mg usa zoloft 50mg ca buy zoloft pills for sale
You really make it seem so easy together with your presentation however I find this topic to be really something which I feel I might never understand. It sort of feels too complicated and very wide for me. I am taking a look forward in your next publish, I will try to get the cling of it!
lasix buy online ventolin generic albuterol usa
cost escitalopram order prozac revia 50mg tablet
order generic augmentin 375mg clomid pill buy clomiphene 50mg online
ipratropium pills buy linezolid 600 mg linezolid 600 mg us
I’m impressed, I must say. Rarely do I encounter a blog that’s equally educative and engaging, and let me tell you, you have hit the nail on the head. The issue is something not enough people are speaking intelligently about. I am very happy that I found this in my search for something concerning this.
Hurrah! After all I got a weblog from where I know how to in fact get helpful data regarding my study and knowledge.
order levitra 10mg generic plaquenil 200mg without prescription cheap plaquenil 400mg
starlix 120mg brand nateglinide 120 mg cheap candesartan online
buy carbamazepine generic lincomycin 500 mg generic buy lincomycin 500mg online
oral cenforce buy aralen online cheap glucophage buy online
PG 소프트
종이 한 장을 꺼내면 종이에는 “나는 아버지를 위해 스웨터를 입습니다”라는 질문이 있습니다.
atorvastatin 80mg cheap lisinopril 5mg without prescription lisinopril pills
Howdy! I just want to give you a huge thumbs up for the great info you’ve got here on this post. I’ll be coming back to your site for more soon.
buy duricef generic buy epivir generic epivir brand
Sweet website , super layout, very clean and utilise friendly.
cabergoline generic buy dostinex 0.25mg online cheap priligy drug
methylprednisolone drug medrol 8mg online purchase clarinex sale
Neotonics is a dietary supplement that offers help in retaining glowing skin and maintaining gut health for its users. It is made of the most natural elements that mother nature can offer and also includes 500 million units of beneficial microbiome.
EndoPeak is a male health supplement with a wide range of natural ingredients that improve blood circulation and vitality.
Glucotrust is one of the best supplements for managing blood sugar levels or managing healthy sugar metabolism.
EyeFortin is a natural vision support formula crafted with a blend of plant-based compounds and essential minerals. It aims to enhance vision clarity, focus, and moisture balance.
Support the health of your ears with 100% natural ingredients, finally being able to enjoy your favorite songs and movies
GlucoBerry is a meticulously crafted supplement designed by doctors to support healthy blood sugar levels by harnessing the power of delphinidin—an essential compound.
buy cytotec for sale buy cheap generic xenical diltiazem 180mg generic
SonoVive™ is a completely natural hearing support formula made with powerful ingredients that help heal tinnitus problems and restore your hearing
BioFit™ is a Nutritional Supplement That Uses Probiotics To Help You Lose Weight
The ingredients of Endo Pump Male Enhancement are all-natural and safe to use.
nootropil 800 mg for sale order generic piracetam purchase anafranil sale
acyclovir ca order generic rosuvastatin 10mg order crestor 20mg without prescription
sporanox 100 mg without prescription buy tindamax 500mg pill order tinidazole generic
Dentitox Pro is a liquid dietary solution created as a serum to support healthy gums and teeth. Dentitox Pro formula is made in the best natural way with unique, powerful botanical ingredients that can support healthy teeth.
HoneyBurn is a 100% natural honey mixture formula that can support both your digestive health and fat-burning mechanism. Since it is formulated using 11 natural plant ingredients, it is clinically proven to be safe and free of toxins, chemicals, or additives.
Neurodrine is a fantastic dietary supplement that protects your mind and improves memory performance. It can help you improve your focus and concentration.
Amiclear is a dietary supplement designed to support healthy blood sugar levels and assist with glucose metabolism. It contains eight proprietary blends of ingredients that have been clinically proven to be effective.
Gorilla Flow is a non-toxic supplement that was developed by experts to boost prostate health for men. It’s a blend of all-natural nutrients, including Pumpkin Seed Extract Stinging Nettle Extract, Gorilla Cherry and Saw Palmetto, Boron, and Lycopene.
TerraCalm is an antifungal mineral clay that may support the health of your toenails. It is for those who struggle with brittle, weak, and discoloured nails. It has a unique blend of natural ingredients that may work to nourish and strengthen your toenails.
GlucoTrust is a revolutionary blood sugar support solution that eliminates the underlying causes of type 2 diabetes and associated health risks.
zetia for sale online sumycin 500mg brand buy cheap generic sumycin
order olanzapine 10mg online cheap diovan 160mg uk valsartan 160mg pill
Thank you, I have just been searching for info
approximately this topic for ages and yours is the
greatest I’ve discovered till now. However, what in regards
to the conclusion? Are you positive concerning the source?
purchase cyclobenzaprine generic buy cyclobenzaprine paypal buy ketorolac generic
colcrys 0.5mg canada order plavix 150mg online methotrexate 5mg uk
best allergy pill fluticasone online best allergy medicine without antihistamine
Buy discount supplements, vitamins, health supplements, probiotic supplements. Save on top vitamin and supplement brands.
Amazed, I’ve reached this milestone with this fascinating story, hats off to the author!
Congratulations on your incredible gift for writing! Your article is an engaging and enlightening read. Wishing you a New Year full of achievements and happiness!
nausea prescription medication list rulide 150 mg ca
Engaging read! As a writer myself, I’d be thrilled to work with you
Good piece! More visuals could make it more dynamic, and my website has some resources that could be useful.
Enjoyed the article. Consider adding more visual aids like images or charts, and take a look at my website for potential ideas.
The article was profound! I’d be honored to contribute my writing.
order sleeping tablets online uk buy melatonin 3mg
Поднимись на волну удачи с игрой Lucky Jet и получи шанс заработать реальные деньги.Лаки Джет – динамичная игра, которая принесет тебе массу эмоций и возможность выиграть крупный приз.
deltasone cost buy deltasone 10mg pills
Stellar content! I’m eager to join as a writer. Can you guide me on applying?
acid reflux drugs prescription list buy irbesartan no prescription
I’m curious if the author is still posting on the blog. We need more information on this topic!
If you wish for to take much from this article then you have to apply such strategies to your won weblog.
Bravo on the article! 👍 The insights are well-expressed, and I believe incorporating more images in your next articles could be beneficial. Have you thought about that? 🖼️
list of prescription acne medication deltasone without prescription acne treatments for teen girls
💫 Wow, blog ini seperti petualangan fantastis meluncur ke alam semesta dari kemungkinan tak terbatas! 💫 Konten yang mengagumkan di sini adalah perjalanan rollercoaster yang mendebarkan bagi pikiran, memicu kagum setiap saat. 🎢 Baik itu teknologi, blog ini adalah sumber wawasan yang menarik! 🌟 Terjun ke dalam pengalaman menegangkan ini dari pengetahuan dan biarkan pemikiran Anda berkelana! 🚀 Jangan hanya mengeksplorasi, rasakan kegembiraan ini! 🌈 Pikiran Anda akan berterima kasih untuk perjalanan menyenangkan ini melalui alam keajaiban yang tak berujung! 🚀
You really make it seem so easy with your presentation but I find this topic to be really something which I think I would never understand. It seems too complicated and very broad for me. I am looking forward for your next post, I will try to get the hang of it!
An intriguing discussion is worth comment. I think that you should publish more about this subject matter, it may not be a taboo
matter but typically folks don’t discuss such topics.
To the next! Best wishes!!
I used to be recommended this website through my cousin. I am now not positive whether this publish is written via him as no one else recognise such special approximately my problem. You are amazing! Thank you!
I’m impressed, I must say. Rarely do I encounter a blog that’s both educative and interesting, and let me tell you, you have hit the nail on the head. The issue is something which not enough people are speaking intelligently about. I am very happy that I found this in my search for something relating to this.
accutane online order absorica online order accutane 20mg generic
Boostaro is a dietary supplement designed specifically for men who suffer from health issues. https://boostarobuynow.us/
GlucoBerry is one of the biggest all-natural dietary and biggest scientific breakthrough formulas ever in the health industry today. This is all because of its amazing high-quality cutting-edge formula that helps treat high blood sugar levels very naturally and effectively. https://glucoberrybuynow.us/
sleep meds prescribed online phenergan for sale
EyeFortin is an all-natural eye-health supplement that helps to keep your eyes healthy even as you age. It prevents infections and detoxifies your eyes while also being stimulant-free. This makes it a great choice for those who are looking for a natural way to improve their eye health. https://eyefortinbuynow.us/
GlucoFlush is an advanced formula specially designed for pancreas support that will let you promote healthy weight by effectively maintaining the blood sugar level and cleansing and strengthening your gut. https://glucoflushbuynow.us/
Herpagreens is a dietary supplement formulated to combat symptoms of herpes by providing the body with high levels of super antioxidants, vitamins
Keratone addresses the real root cause of your toenail fungus in an extremely safe and natural way and nourishes your nails and skin so you can stay protected against infectious related diseases. https://keratonebuynow.us/
Dentitox Pro is a liquid dietary solution created as a serum to support healthy gums and teeth. Dentitox Pro formula is made in the best natural way with unique, powerful botanical ingredients that can support healthy teeth. https://dentitoxbuynow.us/
HoneyBurn is a revolutionary liquid weight loss formula that stands as the epitome of excellence in the industry. https://honeyburnbuynow.us/
Illuderma is a serum designed to deeply nourish, clear, and hydrate the skin. The goal of this solution began with dark spots, which were previously thought to be a natural symptom of ageing. The creators of Illuderma were certain that blue modern radiation is the source of dark spots after conducting extensive research. https://illudermabuynow.us/
buy amoxil tablets amoxicillin 500mg pills amoxicillin order
doxylamine uk over the counter buy provigil 100mg for sale
order azithromycin generic zithromax price azithromycin 500mg oral
furosemide 40mg price furosemide 100mg generic
Решение купить соковыжималку для овощей и фруктов было ключевым моментом в моем пути к здоровому образу жизни. ‘Все соки’ предложили отличный выбор. https://blender-bs5.ru/collection/sokovyzhimalki-dlja-ovoshhej-fruktov – Купить соковыжималку для овощей и фруктов от ‘Все соки’ было лучшим решением для моего здоровья!
prednisolone price buy prednisolone 10mg generic buy omnacortil paypal
Good way of explaining, and good piece of writing to get data concerning my presentation subject matter, which i am going to convey in academy.
Wow! This blog looks exactly like my old one! It’s on a entirely different topic but it has pretty much the same layout and design. Wonderful choice of colors!
order monodox online cheap acticlate for sale
Pretty part of content. I simply stumbled upon your blog and in accession capital to claim that I acquire in fact enjoyed account your blog posts. Any way I’ll be subscribing for your augment or even I achievement you get right of entry to persistently fast.
order albuterol 4mg pills purchase albuterol generic buy allergy pills
visit me, and i will make u satisfied guarantee, make u hard hot
amoxiclav oral purchase amoxiclav sale
buy generic levothyroxine levothyroxine tablet levoxyl over the counter
vardenafil order levitra 10mg canada
doeaccforum.com
Zhu Houzhao는 빨간 눈으로 말했다: “그때 생각이 나서…”
purchase clomid sale buy clomid pills for sale clomiphene 50mg tablet
doeaccforum.com
너무 많은 이야기를 하고 너무 기적적으로 이야기한 후에 Li Dongyang은 관심을 갖게 되었습니다.
order generic semaglutide 14 mg semaglutide generic semaglutide 14mg pill
Aluminium scrap stockpile assessment Recycled aluminium products Aluminium recycling industry insight
agonaga.com
Fang Jifan은 흥분한 Zhu Houzhao를 응시하고 가볍게 물었다.
I couldn’t stop scrolling and reading, your content is truly one-of-a-kind. Thank you for all the time and effort you put into creating such amazing content.
rybelsus cheap purchase rybelsus online buy semaglutide without prescription
Your blog is like a breath of fresh air in a sea of negativity and pessimism Thank you for being a source of light and hope
This post came at just the right time for me Your words have provided me with much-needed motivation and inspiration Thank you
This post hits close to home for me and I am grateful for your insight and understanding on this topic Keep doing what you do
Environmental compliance in metal recycling Scrap aluminium demand forecast Aluminum metal scrap
Metal recycling education, Recycle aluminum cables for cash, Metal recovery services
You should take part in a contest for one of the greatest blogs on the web. I will recommend this blog!
Scrap metal recycling depot Scrap aluminium remelting Aluminum scrap legislation and regulations
Metal waste sorting center, Aluminum cable scrap transportation, Metal scrap reclamation plant
amruthaborewells.com
이 땅에는 밀집된 타타르 족이 돌진하고 있습니다.
Metal waste disposal center Aluminum scrap sales Aluminium recycling carbon credits
Scrap metal recycling depot, Scrap metal prices for aluminum cable, Environmentally friendly scrap metal trading
I needed to put you that tiny word to help thank you so much yet again just for the lovely concepts you’ve contributed on this site. It’s so incredibly generous of people like you to grant freely all a lot of people would have offered for an ebook to generate some money for their own end, certainly since you might well have tried it if you desired. Those good ideas likewise worked to be a easy way to realize that other people online have the identical zeal just like my own to find out more on the subject of this condition. I think there are lots of more fun sessions up front for individuals who start reading your website.
Hey there! This is my first visit to your blog! We are a collection of volunteers and starting a new initiative in a community in the same niche. Your blog provided us useful information to work on. You have done a marvellous job!
Your posts always provide me with a new perspective and encourage me to look at things differently Thank you for broadening my horizons
What makes Sumatra Slim Belly Tonic even more unique is its inspiration from the beautiful Indonesian island of Sumatra. This supplement incorporates ingredients that are indigenous to this stunning island, including the exotic blue spirulina. How amazing is that? By harnessing the power of these rare and natural ingredients, Sumatra Slim Belly Tonic provides you with a weight loss solution that is both effective and enchanting.
Let’s spread the love! Tag a friend who would appreciate this post as much as you did.
GlucoTrust is a powerful dietary supplement that is designed to address the root cause of excessive blood sugar. It provides the body with essential vitamins and minerals that are specifically formulated to lower blood sugar levels and help keep them at optimal levels. This supplement is highly effective in eliminating fat from the liver, pancreas, and cells, which is one of the primary causes of high blood sugar levels. By doing so, it improves the conversion of carbohydrates and proteins into energy that your body can easily burn.
I constantly spent my half an hour to read this weblog’s articles everyday along with a cup of coffee.
Sugar Defender introduces a meticulously curated ensemble of eight key ingredients, each strategically selected to champion healthy blood sugar levels and facilitate weight loss. These ingredients collaborate to enhance the supplement’s effectiveness through diverse mechanisms, including energy elevation, fat burning, and metabolism stimulation, all while providing direct support for maintaining healthy blood glucose levels. Here is an insightful overview of each ingredient along with its purported functionality according to the manufacturer:
Comment récupérer les SMS supprimés sur mobile? Il n’y a pas de corbeille pour les messages texte, alors comment restaurer les messages texte après les avoir supprimés?
I love how you incorporate personal stories and experiences into your posts It makes your content relatable and authentic
I loved as much as you will receive carried out right here. The sketch is tasteful, your authored subject matter stylish. nonetheless, you command get bought an nervousness over that you wish be delivering the following. unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this increase.
I have been struggling with this issue for a while and your post has provided me with much-needed guidance and clarity Thank you so much
The ability of Alpilean to target both subcutaneous and visceral fat distinguishes it from other weight loss products. Subcutaneous fat is visible beneath the skin, whereas visceral fat is harmful fat that accumulates around the organs, increasing the risk of heart disease and other health problems. Alpilean ensures that you not only look better, but also feel better by attacking both types of fat.
Red Boost is a formula that helps a man improve his sexual performance. It is made from natural ingredients and helps a man have more energy for sex. Try Red Boost to have a better experience!
this-is-a-small-world.com
그런 감정의 문장을 애매하게 표현한 후 그는 계속하지 않았습니다.
Scrap metal refinishing Metal scrap processing Iron reclamation operations
Ferrous material performance metrics, Iron disposal solutions, Metal waste repurposing
tsrrub.com
Zhang Heling은 Gu를 경멸했습니다. “죽으면 죽는 것은 별거 아닙니다.”
buy clarinex no prescription generic desloratadine 5mg clarinex 5mg generic
Your blog has become a source of guidance and support for me Your words have helped me through some of my toughest moments
Wow, beautiful site. Thnx … anafranil en vente libre en France
kinoboomhd.com
여기서 살면 돈은 필요없지만.. 평생 못살아요.
Sugar Defender orchestrates a reduction in blood sugar levels through multifaceted pathways. Its initial impact revolves around enhancing insulin sensitivity, optimizing the body’s efficient use of insulin, ultimately leading to a decrease in blood sugar levels. This proactive strategy works to prevent the storage of glucose as fat, mitigating the risk of developing type 2 diabetes.
I was wondering if you ever considered changing the page layout of your site? Its very well written; I love what youve got to say. But maybe you could a little more in the way of content so people could connect with it better. Youve got an awful lot of text for only having one or two images. Maybe you could space it out better?
order orlistat 120mg diltiazem 180mg oral diltiazem 180mg for sale
Metanail Complex is a revolutionary nail and feet care product that aims to promote the health and beauty of your nails.
Outstanding post but I was wanting to know if you could write a litte more on this topic? I’d be very thankful if you could elaborate a little bit further. Thank you!
I love your blog.. very nice colors & theme. Did you design this website yourself or did you hire someone to
do it for you? Plz reply as I’m looking to construct my own blog and would like to find out where
u got this from. thanks a lot
Its like you learn my mind! You seem to understand a lot approximately this, like you wrote the e book in it or something. I think that you simply can do with a few to pressure the message home a little bit, however other than that, that is great blog. A fantastic read. I’ll certainly be back.
sm-slot.com
이것은 후세의 손쉬운 검사와는 다른 지극히 야만적이고 복잡한 과정이다.
hihouse420.com
청년은 경외심을 불러 일으키는 왕 사부를 바라보며 감탄하지 않을 수 없었습니다.
pragmatic-ko.com
Zhu Zaimo는 날카롭게 말했습니다. “이것은 내 명령입니다. 어떻게 감히 불순종합니까?”
sm-online-game.com
그것에 대해 생각한 후 Tang Yin은 “학생들은 반드시 임무를 완수 할 것입니다. “라고 이빨을 비비었습니다.
lfchungary.com
이런 일은 지저분한 계정입니다. 궁전의 미래가 평화롭지 않을까 두렵습니다.
pragmatic-ko.com
아들의 안전을 위해 아버지로서 할 수 있는 일은…
Wow! This could be one particular of the most helpful blogs We have ever arrive across on this subject. Actually Fantastic. I’m also an expert in this topic so I can understand your effort.
sm-slot.com
Hongzhi 황제는 눈살을 찌푸리며 “그래서 쓸모없는 것 같습니까? “라고 말했습니다.
lfchungary.com
나는 거의 병에서 회복되었고 열심히 코딩하고 모든 책 친구들의 지원에 보답하겠습니다.
pragmatic-ko.com
Fang Jifan은 이빨을 비비며 “폐하께서는 사람들을 너무 많이 속이고 계십니다.”
I have been struggling with this issue for a while and your post has provided me with much-needed guidance and clarity Thank you so much
Scrap metal management solutions Ferrous material value-added processes Iron waste reprocessing solutions
Ferrous material audits, Iron recovery depot, Metal recovery and reclaiming solutions
strelkaproject.com
Fang Xiaofan은 다시 경의를 표했습니다. “폐하, Zhongshushe는 누구입니까?”
Your posts always make me feel like I’m not alone in my struggles and insecurities Thank you for sharing your own experiences and making me feel understood
My brother suggested I would possibly like this blog. He was totally right. This publish actually made my day. You cann’t consider just how so much time I had spent for this information! Thank you!
Please let me know if you’re looking for a author for your weblog. You have some really great posts and I believe I would be a good asset. If you ever want to take some of the load off, I’d really like to write some material for your blog in exchange for a link back to mine. Please send me an e-mail if interested. Thank you!
I’m gone to inform my little brother, that he should also go to see this website on regular basis to get updated from most recent gossip.
You’ve made some decent points there. I looked on the web for more info about the issue and found most individuals will go along with your views on this website.
Hello! I’ve been following your website for a while now and finally got the bravery to go ahead and give you a shout out from Huffman Tx! Just wanted to tell you keep up the great job!
Saved as a favorite, I really like your site!
Hey! I know this is somewhat off topic but I was wondering which blog platform are you using for this site? I’m getting tired of WordPress because I’ve had issues with hackers and I’m looking at options for another platform. I would be great if you could point me in the direction of a good platform.
What’s up mates, its impressive article concerning tutoringand fully explained, keep it up all the time.
Please let me know if you’re looking for a author for your site. You have some really great posts and I believe I would be a good asset. If you ever want to take some of the load off, I’d absolutely love to write some material for your blog in exchange for a link back to mine. Please send me an e-mail if interested. Cheers!
What’s up, yeah this post is in fact pleasant and I have learned lot of things from it about blogging. thanks.
If some one wants expert view concerning blogging then i advise him/her to go to see this website, Keep up the nice job.
Wow, that’s what I was seeking for, what a information! present here at this website, thanks admin of this web site.
Unquestionably believe that which you stated. Your favorite justification appeared to be on the internet the simplest thing to be aware of. I say to you, I definitely get irked while people consider worries that they plainly do not know about. You managed to hit the nail upon the top and also defined out the whole thing without having side effect , people can take a signal. Will likely be back to get more. Thanks
Great delivery. Outstanding arguments. Keep up the amazing work.
Nice blog here! Also your website lots up fast! What host are you using? Can I am getting your associate link in your host? I desire my website loaded up as fast as yours lol
Greetings! Very helpful advice within this article! It is the little changes which will make the largest changes. Thanks a lot for sharing!
There is definately a lot to know about this subject. I love all the points you’ve made.
When someone writes an post he/she keeps the idea of a user in his/her mind that how a user can understand it. Thus that’s why this piece of writing is great. Thanks!
pchelografiya.com
그래서 긴장하면서도 설레는 마음이 더 크다.
Metal scrap recovery solutions Ferrous scrap resource conservation Iron and steel recycling and reclamation yard
Ferrous scrap recuperation, Iron scrap recovery center, Metal waste management services
strelkaproject.com
이런 종류의 전쟁은 수많은 문명을 악몽으로 여겼습니다.
Metal waste reclamation yard Ferrous material treatment Iron scrap reclaimer
Ferrous scrap quality assurance, Iron waste reclaiming depot, Metal recycling and recovery facility
I discovered your weblog web site on google and examine a couple of of your early posts. Proceed to maintain up the very good operate. I just extra up your RSS feed to my MSN News Reader. Looking for ahead to studying extra from you later on!?
It?s actually a great and helpful piece of information. I?m glad that you shared this useful information with us. Please keep us up to date like this. Thanks for sharing.
It means so much to receive positive feedback and know that my content is appreciated. I strive to bring new ideas and insights to my readers.
Almanya medyum haluk hoca sizlere 40 yıldır medyumluk hizmeti veriyor, Medyum haluk hocamızın hazırladığı çalışmalar ise berlin medyum papaz büyüsü, Konularında en iyi sonuç ve kısa sürede yüzde yüz için bizleri tercih ediniz. İletişim: +49 157 59456087
yangsfitness.com
그러나 이때 내시가 왔다. “폐하, 취안 저우가보고하러 왔습니다.”
danatoto alternatif link!
Terpercaya
wonderful submit, very informative. I wonder why the other experts of this sector do not understand this. You should continue your writing. I am sure, you have a huge readers’ base already!
yangsfitness.com
Liu Jian은 또한 얼굴이 찡그린 채 주먹을 쥐고 손바닥이 이미 젖었습니다.
Couldn’t agree more with the praises above; this post is wonderful!
Scrap metal repurposing center Ferrous waste recycling center Iron waste disposal
Ferrous material plant operations, Iron scrap utilization, Scrap metal baling services
mega-casino66.com
그는 수십 년 동안 정치에 종사했기 때문에 Zhu Houzhao가 말한 것이 사실임을 자연스럽게 알고 있습니다.
Güvenilir bir danışman için medyum nasip hocayı seçin en iyi medyum hocalardan bir tanesidir.
These are really wonderful ideas in concerning blogging. You have touched some pleasant factors here. Any way keep up wrinting.
I all the time emailed this blog post page to all my associates, because if like to read it then my friends will too.
Excellent blog here! Also your site rather a lot up fast! What host are you the use of? Can I am getting your associate link for your host? I want my website loaded up as fast as yours lol
Howdy! Do you know if they make any plugins to help with SEO? I’m trying to get my blog to rank for some targeted keywords but I’m not seeing very good gains. If you know of any please share. Cheers!
When someone writes an piece of writing he/she keeps the thought of a user in his/her mind that how a user can understand it. So that’s why this piece of writing is amazing. Thanks!
Greetings from Carolina! I’m bored to death at work so I decided to check out your website on my iphone during lunch break. I really like the knowledge you present here and can’t wait to take a look when I get home. I’m shocked at how quick your blog loaded on my mobile .. I’m not even using WIFI, just 3G .. Anyhow, amazing site!
It’s remarkable designed for me to have a web site, which is helpful in favor of my knowledge. thanks admin
I like the valuable information you provide in your articles. I will bookmark your weblog and check again here frequently. I am quite certain I will learn lots of new stuff right here! Good luck for the next!
This is a good tip especially to those new to the blogosphere. Brief but very accurate information Thank you for sharing this one. A must read article!
Yes! Finally something about %keyword1%.
I’m impressed, I must say. Rarely do I encounter a blog that’s both educative and engaging, and let me tell you, you have hit the nail on the head. The issue is something not enough folks are speaking intelligently about. I’m very happy that I found this in my search for something concerning this.
It is perfect time to make some plans for the future and it is time to be happy. I have read this post and if I could I want to suggest you few interesting things or advice. Perhaps you could write next articles referring to this article. I want to read more things about it!
I got this web site from my pal who informed me regarding this website and now this time I am visiting this web site and reading very informative posts at this place.
It’s awesome to go to see this web site and reading the views of all mates regarding this post, while I am also eager of getting knowledge.
Hi, after reading this awesome post i am too cheerful to share my familiarity here with friends.
ttbslot.com
나쁜 사람들의 속임수는 이해하기 쉽지만 He Tingyang은 누구입니까?
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to more added agreeable from you! By the way, how can we communicate?
qiyezp.com
Liang Chu는 거의 발을 밟을 뻔했습니다. “Fang 가족에게 선물도 가져 왔습니다.”
fantastic morning beginning with an excellent read 📖🌅
sandyterrace.com
Chang Cheng은 “Zhao 형제…I…I…”라고 외쳤습니다.
Güvenilir bir danışman için medyum nasip hocayı seçin en iyi medyum hocalardan bir tanesidir.
The best thing is that you can use the live cam technology yourself and interact with the women in the chat – all you need is a free chat with cam girls live account and your own cam.
sandyterrace.com
Fang Jifan은 깜짝 놀랐고 Zhu Houzhao와 Liu Jianren 등을 쳐다볼 수밖에 없었습니다.
Güvenilir bir danışman için medyum haluk hocayı seçin en iyi medyum hocalardan bir tanesidir.
freeflowincome.com
Fang Jifan은 눈살을 찌푸리며 “가족 중에 공부하는 자녀가 있습니까? “라고 말했습니다.
Güvenilir bir danışman için medyum haluk hocayı seçin en iyi medyum hocalardan bir tanesidir.
Howdy! This is kind of off topic but I need some advice from an established blog. Is it tough to set up your own blog? I’m not very techincal but I can figure things out pretty fast. I’m thinking about setting up my own but I’m not sure where to begin. Do you have any points or suggestions? With thanks
donmhomes.com
非常に興味深い内容でした。新たな発見があります。
I am incessantly thought about this, regards for putting up.
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! By the way, how can we communicate?
What Is Puravive? Puravive is a natural weight loss supplement that is known to boost the metabolic processes of the body.
Howdy I am so happy I found your site, I really found you by mistake, while I was searching on Askjeeve for something else, Anyhow I am here now and would just like to say many thanks for a incredible post and a all round enjoyable blog (I also love the theme/design), I dont have time to read through it all at the minute but I have book-marked it and also included your RSS feeds, so when I have time I will be back to read much more, Please do keep up the excellent b.
I?¦ve recently started a blog, the info you offer on this site has helped me tremendously. Thanks for all of your time & work.
Hey there, You have done a fantastic job. I?ll certainly digg it and in my view suggest to my friends. I’m sure they’ll be benefited from this website.
Thanks for the tips you share through this web site. In addition, numerous young women which become pregnant do not even aim to get health insurance coverage because they worry they wouldn’t qualify. Although many states at this point require that insurers provide coverage irrespective of the pre-existing conditions. Rates on these guaranteed options are usually greater, but when thinking about the high cost of medical treatment it may be any safer strategy to use to protect one’s financial future.
cougarsbkjersey.com
この記事の実用性に感動しました。大変役立つ情報をありがとうございます。
certainly like your website however you need to check the spelling on quite a few of your posts. Many of them are rife with spelling problems and I find it very troublesome to tell the reality however I?ll definitely come back again.
Good day! I know this is kinda off topic but I’d figured I’d ask. Would you be interested in exchanging links or maybe guest authoring a blog post or vice-versa? My blog covers a lot of the same topics as yours and I believe we could greatly benefit from each other. If you happen to be interested feel free to shoot me an e-mail. I look forward to hearing from you! Fantastic blog by the way!
Hello there, just became aware of your blog through Google, and found that it is truly informative. I’m going to watch out for brussels. I’ll be grateful if you continue this in future. Numerous people will be benefited from your writing. Cheers!
Boostaro is a natural dietary supplement for male health, enhancing circulation and overall bodily functions. Supports wellness with natural ingredients.
FitSpresso™ is a nutritional supplement that uses probiotics to help you lose weight.
ZenCortex Research’s contains only the natural ingredients that are effective in supporting incredible hearing naturally.A unique team of health and industry professionals dedicated to unlocking the secrets of happier living through a healthier body.
Sight Care is a natural formula that can support healthy eyesight by focusing the root of the problem. Sight Care can be useful to make better your vision.
Are you seeking for a way to feel better? Unlock the trusted source for health and wellness right here! All of your health issues and difficulties must be addressed using the key.
I have figured out some important things through your website post. One other thing I would like to mention is that there are lots of games that you can buy which are designed specifically for toddler age young children. They include things like pattern identification, colors, animals, and shapes. These usually focus on familiarization as an alternative to memorization. This makes children engaged without feeling like they are studying. Thanks
cougarsbkjersey.com
素敵な記事で、読んでいてとても楽しかったです。
Thanks for your tips about this blog. One thing I want to say is the fact that purchasing gadgets items in the Internet is nothing new. In fact, in the past 10 years alone, the market for online gadgets has grown significantly. Today, you’ll find practically virtually any electronic gizmo and devices on the Internet, from cameras plus camcorders to computer elements and game playing consoles.
lacolinaecuador.com
Wang Ao는 절을 할 수밖에 없었습니다. “피험자는 죽었습니다. 지금은 … 지금입니다 …”
Good – I should certainly pronounce, impressed with your site. I had no trouble navigating through all the tabs as well as related info ended up being truly simple to do to access. I recently found what I hoped for before you know it at all. Quite unusual. Is likely to appreciate it for those who add forums or anything, site theme . a tones way for your customer to communicate. Nice task..
En iyi medyum olarak bir danışman için medyum haluk hocayı seçin en iyi medyum hocalardan bir tanesidir.
thebuzzerpodcast.com
그런 다음 그는 머리를 숙이며 말했다.
Simply wish to say your article is as astounding. The clarity in your post is simply excellent and i could assume you are an expert on this subject. Well with your permission let me to grab your feed to keep updated with forthcoming post. Thanks a million and please keep up the enjoyable work.
cougarsbkjersey.com
非常に興味深い記事でした。新たな知識をありがとう。
tvlore.com
폐하는 자신을 위해 일반 사설을 끊었습니다. 정말 큰 문제입니다.
I am curious to find out what blog system you happen to be utilizing? I’m experiencing some minor security problems with my latest site and I would like to find something more secure. Do you have any solutions?
I am usually to running a blog and i actually admire your content. The article has really peaks my interest. I’m going to bookmark your website and keep checking for brand new information.
I really like looking through and I conceive this website got some truly utilitarian stuff on it! .
cougarsbkjersey.com
素晴らしい洞察と分析。これからも素晴らしい記事を期待しています。
Hello there, just became aware of your blog through Google, and found that it is really informative. I’m gonna watch out for brussels. I will be grateful if you continue this in future. Many people will be benefited from your writing. Cheers!
bestmanualpolesaw.com
이 학교에서 죽음의 평온이 회복되었습니다.
you’re really a good webmaster. The site loading speed is amazing. It seems that you’re doing any unique trick. Also, The contents are masterpiece. you’ve done a magnificent job on this topic!
I carry on listening to the news update speak about receiving free online grant applications so I have been looking around for the finest site to get one. Could you tell me please, where could i acquire some?
My spouse and I absolutely love your blog and find a lot of your post’s to be just what I’m looking for. Would you offer guest writers to write content in your case? I wouldn’t mind creating a post or elaborating on a number of the subjects you write with regards to here. Again, awesome blog!
freeflowincome.com
두 짐승 인 Zhang Heling과 Zhang Yanling은 실제로 황제에게 모든 씨족을 소집하여 베이징에 정착하도록 요청했습니다.
whoah this blog is excellent i love reading your articles. Keep up the good work! You know, lots of people are searching around for this info, you can help them greatly.
Almanya’nın En iyi medyum olarak bir danışman için medyum haluk hocayı seçin en iyi medyum hocalardan bir tanesidir.
buysteriodsonline.com
그것에 대해 생각한 후 Zhu Houzhao는 “Fang Jifan은 Xu Jing을 믿고 내 아들은 Fang Jifan을 믿습니다. “라고 말했습니다.
オンカジ k8
読んでいて心が動かされました。共有せずにはいられません!
largestcatbreed.com
그는 경멸하는 듯한 미소를 지으며 설명을 마친 뒤 사당으로 걸어갔다.
Renew is a nutritional supplement launched in 2024 to help anyone lose weight.
k8 カジノ 出金
実用性抜群の内容で、とても有益でした。ありがとうございます。
Hi I am so glad I found your site, I really found you by error, while I was researching on Askjeeve for something else, Regardless I am here now and would just like to say thanks a lot for a marvelous post and a all round exciting blog (I also love the theme/design), I don’t have time to go through it all at the minute but I have saved it and also included your RSS feeds, so when I have time I will be back to read a great deal more, Please do keep up the excellent job.
Can I just say what a reduction to search out someone who actually is aware of what theyre speaking about on the internet. You undoubtedly know the right way to carry a problem to gentle and make it important. More folks need to read this and perceive this aspect of the story. I cant consider youre no more well-liked since you positively have the gift.
k8 かじ の
毎回このブログを読むのが楽しみです。素敵な記事をありがとう。
I found your weblog website on google and check just a few of your early posts. Proceed to keep up the very good operate. I just additional up your RSS feed to my MSN Information Reader. In search of forward to studying more from you later on!…
whoah this weblog is excellent i love studying your articles. Stay up the great paintings! You realize, many persons are hunting around for this information, you could help them greatly.
This is hands down one of the finest articles I’ve read on this topic! The author’s extensive knowledge and passion for the subject are evident in every paragraph. I’m so thankful for coming across this piece as it has enriched my comprehension and stimulated my curiosity even further. Thank you, author, for taking the time to create such a outstanding article!
k8 パチンコ
とても有益な情報で満載でした。大変役に立ちました。
Wow, incredible blog layout! How long have you been blogging for? you make blogging look easy. The overall look of your web site is excellent, as well as the content!
I not to mention my buddies came reviewing the best procedures located on your website and then immediately came up with a horrible suspicion I never expressed respect to the web site owner for those strategies. All the people happened to be consequently very interested to study them and already have without a doubt been tapping into these things. Appreciate your actually being indeed considerate and for pick out such terrific subject areas most people are really eager to learn about. Our own sincere regret for not expressing appreciation to earlier.
Utterly indited content, thankyou for selective information.
Hi there, I found your web site via Google while searching for a related topic, your web site came up, it looks good. I’ve bookmarked it in my google bookmarks.
I have noticed that over the course of building a relationship with real estate managers, you’ll be able to come to understand that, in every real estate transaction, a percentage is paid. In the end, FSBO sellers really don’t “save” the payment. Rather, they struggle to earn the commission by means of doing a great agent’s work. In doing so, they commit their money in addition to time to perform, as best they might, the responsibilities of an realtor. Those responsibilities include displaying the home by means of marketing, representing the home to prospective buyers, creating a sense of buyer desperation in order to prompt an offer, arranging home inspections, controlling qualification inspections with the lender, supervising repairs, and facilitating the closing of the deal.
k8 カジノ レート
実用的な情報が豊富で、とても参考になる素晴らしい記事です。
I’m not sure why but this site is loading incredibly slow for me. Is anyone else having this issue or is it a issue on my end? I’ll check back later on and see if the problem still exists.
Hi there, just was alert to your blog thru Google, and located that it’s really informative. I am gonna be careful for brussels. I’ll appreciate if you continue this in future. Lots of other folks will likely be benefited from your writing. Cheers!
You are my inhalation, I possess few blogs and occasionally run out from post :). “The soul that is within me no man can degrade.” by Frederick Douglas.
Very interesting subject , thankyou for putting up.
Reading The work is like catching up with an old friend; comfortable, enlightening, and always welcome.
The grace and authority with which you handle topics are awe-inspiring. I always come away with new knowledge.
I have observed that online education is getting well-known because obtaining your degree online has turned into a popular selection for many people. Quite a few people have definitely not had an opportunity to attend an established college or university although seek the improved earning possibilities and a better job that a Bachelor Degree provides. Still people might have a college degree in one course but wish to pursue one thing they now have an interest in.
F*ckin? amazing issues here. I?m very satisfied to look your post. Thanks so much and i’m taking a look ahead to contact you. Will you please drop me a e-mail?
You navigate through topics with such grace, it’s like watching a dance. Care to teach me a few steps?
Yet another issue is that video games are typically serious naturally with the principal focus on knowing things rather than leisure. Although, there’s an entertainment aspect to keep your young ones engaged, each one game is often designed to develop a specific expertise or program, such as numbers or scientific disciplines. Thanks for your post.
k8 スポーツ ブック
このブログを読むたびに、新たな発見があります。素晴らしい!
Another thing I’ve really noticed is for many people, bad credit is the reaction of circumstances outside of their control. For instance they may have already been saddled through an illness and as a consequence they have higher bills for collections. It would be due to a work loss or the inability to do the job. Sometimes separation and divorce can really send the funds in an opposite direction. Thanks sharing your thinking on this blog site.
Great beat ! I would like to apprentice while you amend your web site, how could i subscribe for a blog web site? The account helped me a acceptable deal. I had been tiny bit acquainted of this your broadcast provided bright clear concept
Nice read, I just passed this onto a friend who was doing some research on that. And he just bought me lunch as I found it for him smile So let me rephrase that: Thank you for lunch!
magnificent points altogether, you just gained a brand new reader. What would you recommend about your post that you made some days ago? Any positive?
主役は銭形2 (V2.2)
素晴らしい洞察力と情報の提供、本当にありがとうございます。
I’m delighted by your post and its celebration of this wonderful Monday. The content is both insightful and uplifting. Adding more visuals could make it even more engaging for a wider audience.
This post will help the internet viewers for building up new weblog or even a blog from start to end.
Do you mind if I quote a couple of your posts as long as I provide credit and sources back to your website? My website is in the exact same area of interest as yours and my users would genuinely benefit from a lot of the information you provide here. Please let me know if this okay with you. Cheers!
freeflowincome.com
Ouyang Zhifang은 “계산되었으며 은화 이십 이만 냥이 필요합니다. “라고 말했습니다.
In the grand scheme of things you’ll receive a B+ just for effort and hard work. Where you actually confused everybody ended up being in all the specifics. You know, people say, details make or break the argument.. And that could not be much more correct right here. Having said that, permit me say to you what exactly did give good results. Your text can be pretty convincing and that is most likely the reason why I am making the effort in order to comment. I do not make it a regular habit of doing that. Next, whilst I can notice a leaps in reason you come up with, I am not really sure of exactly how you seem to connect the details which inturn help to make the final result. For now I will, no doubt yield to your position but wish in the near future you actually link your facts better.
Some truly interesting details you have written.Helped me a lot, just what I was looking for : D.
nikontinoll.com
“눈으로 직접 보셨나요?” 홍지황제는 주후조와 팡지판을 바라보며 미소를 지었다.
Lovely just what I was looking for.Thanks to the author for taking his clock time on this one.
AGENCANTIK
AGENCANTIK says Thank you very much, all the information above is very good and interesting
Hmm it looks like your website ate my first comment (it was extremely long) so I guess I’ll just sum it up what I wrote and say, I’m thoroughly enjoying your blog. I too am an aspiring blog blogger but I’m still new to everything. Do you have any helpful hints for beginner blog writers? I’d really appreciate it.
I do agree with all the ideas you’ve presented in your post. They are really convincing and will certainly work. Still, the posts are too short for starters. Could you please extend them a little from next time? Thanks for the post.
I take pleasure in, lead to I found exactly what I used to be looking for. You have ended my 4 day long hunt! God Bless you man. Have a nice day. Bye
F*ckin? tremendous things here. I am very glad to see your post. Thanks a lot and i’m looking forward to contact you. Will you kindly drop me a mail?
Remarkable post! The author’s skills are commendable!
파워 오브 토르 메가웨이즈
Fang Jifan은 모든 최악의 가능성을 생각하며 몸을 떨었습니다.
F*ckin’ remarkable things here. I’m very glad to see your post. Thanks a lot and i’m looking forward to contact you. Will you kindly drop me a e-mail?
게이츠 오브 올림푸스
Hongzhi 황제는 감동적으로 말했습니다. “와서 저를 지원하십시오.”
리액툰즈
거의 말할 수 있습니다 … Fang Jifan은 많은 관심을 기울이지 않았지만.
I always spent my half an hour to read this webpage’s posts everyday along with a cup of coffee.
더 도그 하우스 메가웨이즈
더 겸손하고 입을 다물고 있으면 사실 꽤 좋습니다.
The subsequent time I read a blog, I hope that it doesnt disappoint me as a lot as this one. I imply, I know it was my choice to read, however I actually thought youd have something interesting to say. All I hear is a bunch of whining about something that you could repair should you werent too busy in search of attention.
북 오브 데드
현재 막부는 상황에 대한 통제력을 다소 상실했습니다.
블랙 맘바
Wu Xiong은 당황했습니다. “문제 … 뭐 … 무슨 문제.”
Write more, thats all I have to say. Literally, it seems as though you relied on the video to make your point. You definitely know what youre talking about, why waste your intelligence on just posting videos to your site when you could be giving us something enlightening to read?
Woah! I’m really loving the template/theme of this site. It’s simple, yet effective. A lot of times it’s tough to get that “perfect balance” between superb usability and visual appeal. I must say you have done a amazing job with this. In addition, the blog loads very fast for me on Internet explorer. Superb Blog!
Wow, marvelous weblog format! How long have you been running a blog for? you make running a blog look easy. The total look of your website is wonderful, let alone the content material!
에그벳 주소
Hongzhi 황제는이 거대한 물고기의 골격을 복원하여 Jingshan에 전시하도록 명령했습니다.
Hi there everyone, it’s my first pay a visit at this web site, and post is in fact fruitful for me, keep up posting such articles.
무료 슬롯 사이트
포대에서 포병들은 포병의 마지막 검사를 수행했습니다.
What is Sugar Defender 24? Jeffrey Mitchell made the Sugar Defender 24. It is a product (Sugar Defender Diabetes) that helps your blood sugar health.
Exceptional! But seriously, why all the English comments and emojis? 😅
돌리고 슬롯
그는 자신이 10년 넘게 황제를 지냈지만 다른 사람들에게 진정으로 평가받은 적이 없다고 자문했습니다.
This blog is definitely rather handy since I’m at the moment creating an internet floral website – although I am only starting out therefore it’s really fairly small, nothing like this site. Can link to a few of the posts here as they are quite. Thanks much. Zoey Olsen
게이츠 오브 올림푸스
Zhang Sen은 그의 그랜드 마스터를 경외심으로 바라보았고, 이 사람은 그가 존경하는 존재였습니다.
Hola! I’ve been reading your web site for some time now and finally got the bravery to go ahead and give you a shout out from Humble Tx! Just wanted to say keep up the fantastic job!
플레이 슬롯
한 무리의 아이들이 Zhu Zaimo와 함께 즉시 흩어졌습니다.
Hey! This is kind of off topic but I need some advice from an established blog. Is it tough to set up your own blog? I’m not very techincal but I can figure things out pretty fast. I’m thinking about creating my own but I’m not sure where to start. Do you have any points or suggestions? Thank you
Thank you for another informative web site. Where else could I get that kind of info written in such an ideal way? I have a project that I am just now working on, and I have been on the look out for such info.
Nice post. I learn something more challenging on different blogs everyday. It will always be stimulating to read content from other writers and practice a little something from their store. I’d prefer to use some with the content on my blog whether you don’t mind. Natually I’ll give you a link on your web blog. Thanks for sharing.
안전한 슬롯 사이트
Zhu Houzhao는 “운명은 영원하며 유덕 한 사람 만이 거기에 산다! “라고 말했습니다.
플레이 슬롯
“잔의 벤공이야…” 주후조는 무슨 말을 하고 싶은 듯 얼굴을 빤히 쳐다보았다.
There is noticeably a bundle to know about this. I assume you made certain nice points in features also.
블랙 맘바
갑작스런 포효에 경비원들은 깜짝 놀라서 무의식적으로 뒤로 물러났다.
Hmm is anyone else encountering problems with the images on this blog loading? I’m trying to find out if its a problem on my end or if it’s the blog. Any suggestions would be greatly appreciated.
Well I sincerely liked studying it. This post offered by you is very effective for proper planning.
슬롯 게임 사이트
Ouyang Zhi는 여전히 무표정한 얼굴을 가지고 있었고 여전히 예측할 수 없었습니다.
What i do not understood is actually how you are not really much more neatly-appreciated than you might be now. You are so intelligent. You know thus significantly in terms of this matter, made me in my view believe it from so many various angles. Its like women and men are not fascinated unless it?s something to do with Girl gaga! Your personal stuffs nice. Always take care of it up!
An fascinating discussion is worth comment. I think that you need to write more on this subject, it won’t be a taboo subject but typically people are not sufficient to speak on such topics. To the next. Cheers
AGENCANTIK
AGENCANTIK says wow such a good post !
슬롯 5 만
경제를 실제로 관찰한 적이 없는 사람이 이것을 어떻게 이해할 수 있습니까?
마종 웨이즈
Hongzhi 황제는 눈살을 찌푸 렸습니다. “일본 경비대가 일본을 진압 할 수 없다면 누가 할 수 있습니까?”
Hiya very nice website!! Guy .. Beautiful .. Amazing .. I will bookmark your website and take the feeds also? I am satisfied to find so many useful information here in the publish, we’d like develop more strategies in this regard, thank you for sharing. . . . . .
http://proscooters.ru/index.php?action=profile;area=forumprofile
http://gm6699.com/home.php?mod=space&uid=3016422
슬롯 먹튀 사이트
즉, 사고가 났을 때 생명을 구할 수 있는지 여부는 전적으로 하나님의 뜻에 달려 있습니다.
Wow, incredible blog format! How long have you been blogging for? you make blogging glance easy. The full glance of your site is magnificent, let alonewell as the content!
https://www.google.at/url?q=https://output.jsbin.com/wipugasaho/
황제 슬롯
그런 결론에 직면한 팡지판은 할 말이 없었다.
https://freebookmarkstore.win/story.php?title=shattered-no-more-a-guide-to-auto-glass-replacement#discuss
https://shorl.com/vifastistuvumu
안전한 슬롯 사이트
Li Dongyang은 항상 매우 현명했고 폐하의 기질을 잘 이해하지 못했습니다.
Good write-up, I¦m normal visitor of one¦s site, maintain up the nice operate, and It’s going to be a regular visitor for a lengthy time.
슬롯 용가리
그는 이 사람들을 알고, 그들 모두를 알고 있습니다… 거의 모든 사람들이 밤낮으로 함께했습니다.
Автомойка самообслуживания под ключ становится всё популярнее. Это экономичный и простой способ начать своё дело с минимальными вложениями.
Today, I went to the beachfront with my children. I found a sea shell and gave it to my 4 year old daughter and said “You can hear the ocean if you put this to your ear.” She placed the shell to her ear and screamed. There was a hermit crab inside and it pinched her ear. She never wants to go back! LoL I know this is entirely off topic but I had to tell someone!
에그벳300
이 세대의 왕 전하가 Tianhuang의 지위에 의존하여 자신을 고소할지 하나님은 아십니다.
토토 캔 배당 분석
전투에 강한 선원들은 마침내 마음의 동요를 억제했습니다.
Luar biasa sekali! ❤️ Apakah penulisnya dibayar? Saya tertarik untuk bergabung!
미성년자 토토 사이트
Fang Jifan은 “폐하, 계획이 있습니다. 시도해 볼 수 있습니다.”
AGENCANTIK
AGENCANTIK says I used to be checking constantly your website.
Awesome! Its really awesome article, I have got much clear idea concerning from this post.
아시아 슬롯
반면 Zhu Houzhao는 명확한 경계선을 그은 것처럼 보였고 악을 질투했습니다.
토토 사이트 검증
Fang Jifan은 Hongzhi 황제의 얼굴에서 이상한 표정을 보았고 “폐하 …”라고 말하지 않을 수 없었습니다.
하이브 슬롯
즉, 그는 사람을 바보나 미치광이로 생각하지 않는다.
Hey very nice site!! Man .. Beautiful .. Amazing .. I’ll bookmark your blog and take the feeds also?I am happy to find a lot of useful information here in the post, we need work out more techniques in this regard, thanks for sharing. . . . . .
토토 검증
Zhu Houzhao는 고개를 끄덕이며 “그게 다야”라고 말했습니다.
Hmm is anyone else experiencing problems with the images on this blog loading? I’m trying to figure out if its a problem on my end or if it’s the blog. Any responses would be greatly appreciated.
Great write-up, I am regular visitor of one?s blog, maintain up the excellent operate, and It is going to be a regular visitor for a long time.
I do love the manner in which you have framed this particular challenge and it really does provide us some fodder for thought. However, because of what precisely I have observed, I basically wish when other opinions pack on that individuals stay on point and in no way start on a soap box involving the news du jour. Yet, thank you for this excellent point and although I do not concur with it in totality, I regard your viewpoint.
Sweet website , super layout, really clean and use genial.
Thank you for the sensible critique. Me and my neighbor were just preparing to do a little research about this. We got a grab a book from our local library but I think I learned more from this post. I’m very glad to see such wonderful info being shared freely out there.
슬롯 온라인
제자와 손자를 받아들일 때 상대방의 배경을 먼저 묻지 말고 먼저 인물을 보라.